The Mathematics and Science of Cryptography
- Joe Jun Tan
- Mar 23
- 4 min read
Introduction
Cryptography, used for secure communication, can be traced back thousands of years to ancient civilizations, including Ancient Egypt, where modified hieroglyphics were used to obscure the meaning of important inscriptions. In modern day, cryptography plays an important role in everyday life, yet it often goes unnoticed. Every time a message is sent, a website is logged into, or an online purchase is made, cryptography is working in the background to keep information safe, secure, and private. Cryptography is the science and mathematics of securing information so that only authorized people can access it. Modern cryptography depends on carefully designed algorithms and mathematical problems that are easy to perform but extremely challenging to reverse. These ideas allow individuals around the world to communicate securely, even over public networks like the internet.

Cryptography uses the idea of transforming information into a form that cannot be understood alone; it must be accompanied by a special key. The original legible message is called “plaintext”, and the scrambled version is called “ciphertext”. Encryption is the procedure of converting plaintext into ciphertext, while decryption is the inverse of this process. The main goals of cryptography are confidentiality, integrity, authentication, and non-repudiation. Confidentiality ensures that information is kept private, integrity ensures that information is not altered, authentication verifies the identity of users, and non-repudiation prevents the denial of sending a message. These goals are achieved using a combination of mathematics, computer science, and careful system design.


The Two Major Types of Cryptography
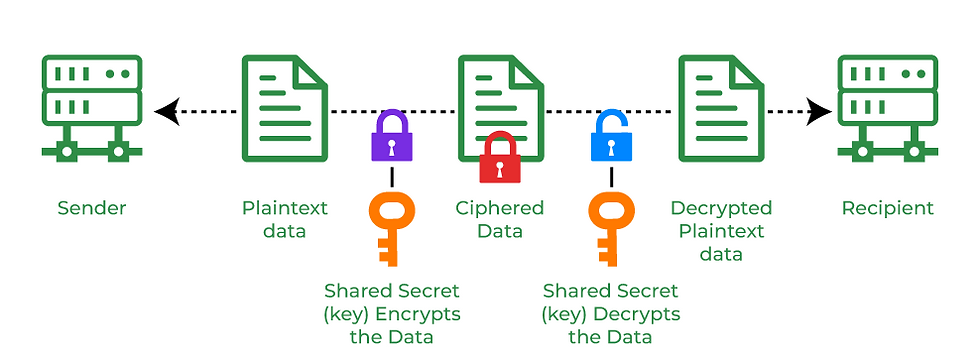
One major type of cryptography is symmetric cryptography. Symmetric cryptography utilizes one shared key for both encryption and decryption, meaning both parties must know the same secret key. Symmetric encryption is very efficient; it is commonly used for encrypting large quantities of data such as files, videos, or records. One of the most widely used symmetric encryption algorithms today is the Advanced Encryption Standard (AES). AES works by organizing data into blocks and continuously applying mathematical transformations such as substitution, permutation, and modular arithmetic. These steps mix the data thoroughly, making patterns extremely difficult to detect. The security of AES does not rely on hiding the algorithm itself; instead, it depends on the secrecy and randomness of the encryption key. Without the correct key, trying to reverse the encryption would require brute force testing of an impossibly large number of possibilities, which is computationally infeasible.
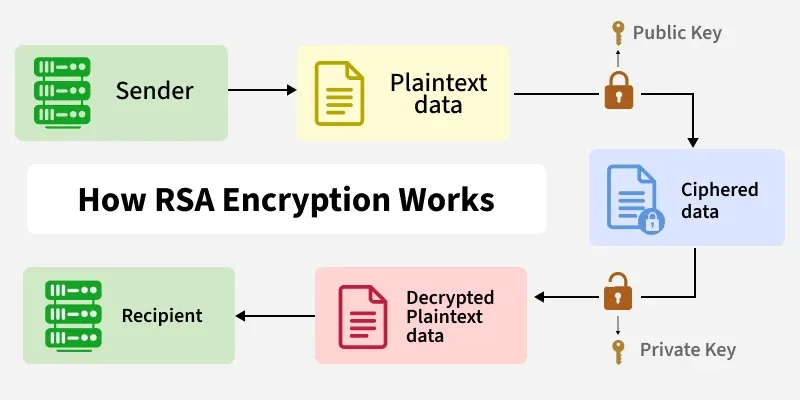
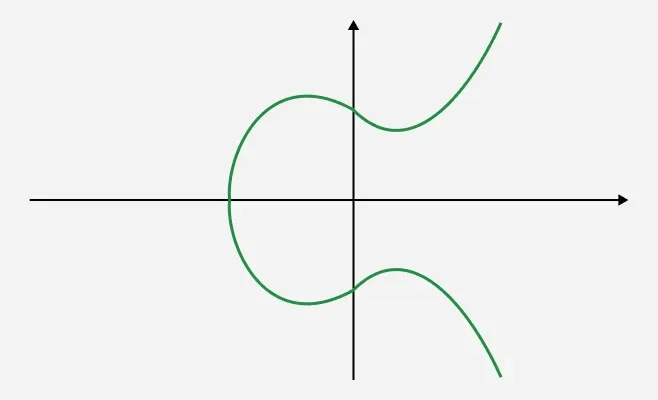
Another major form of cryptography, called asymmetric cryptography or public-key cryptography, relies on a pair of keys, one public and one private, that are connected mathematically. While the public key can be freely shared, only the associated private key can decrypt data encrypted with the public key, so the private key must remain confidential. Though slower than symmetric cryptography, asymmetric cryptography solves the major problem: you do not need to secretly share a key beforehand. This means two people who have never met can still communicate securely online. Two important examples of asymmetric cryptography are RSA and Elliptic Curve Cryptography (ECC). The security of RSA comes from the fact that factoring very large numbers into prime numbers is computationally difficult. While multiplying two large prime numbers is easy, reversing the process is extremely difficult for computers. ECC relies on the mathematics of elliptic curves and offers similar security with much smaller keys, making it efficient and widely used for modern devices.
Image Credit: GeeksforGeeks
The Math and Science Behind Cryptography
Cryptography relies on several key mathematical concepts that make encryption secure. One concept is prime numbers, which are numbers that can only be divided by 1 and themselves. Large prime numbers are used in key generation because they create mathematical problems that are hard to reverse. This idea is essential for algorithms like RSA. Another concept, modular arithmetic, sometimes called “clock math,” works with remainders after division. For example, in modulo 12 arithmetic, adding 9 and 5 results in 2. Cryptographic algorithms rely heavily on modular arithmetic because it produces results that appear random and are difficult to predict. A one-way function is also a key concept in cryptography. One-way functions are easy to compute but very difficult to reverse. These functions are the structure of password hashing (scrambling), which is designed to be irreversible, ensuring that sensitive data cannot be tampered with even if the hashed data is exposed. Even with powerful computers, reversing these functions without the correct key would take an unthinkable amount of time.
Cryptography is not just about mathematical equations; it is also a science that studies how systems behave under and respond to attack. Cryptographers analyze potential weaknesses, test algorithms against real-world threats, and constantly improve security methods. Randomness, or entropy, is another important scientific principle in cryptography. Strong encryption requires random keys, since keys that are not random and predictable can be easily uncovered by invaders. Modern systems use physical processes and hardware-based random number generators to ensure true and high-quality randomness.
Challenges and Implications of Cryptography
One of the biggest challenges cryptography faces today is the development of quantum computers. Quantum algorithms could theoretically break systems like RSA and ECC by solving their underlying math problems much faster than classical computers. To prepare for this possibility, researchers are developing post-quantum cryptography. These new algorithms are designed to resist attacks from both classical and quantum computers. Many organizations are currently working to improve and standardize quantum-resistant cryptographic systems.
Cryptography is a powerful combination of mathematics and science that makes secure communication possible in the digital age. From symmetric encryption that protects large amounts of data to asymmetric systems that enable secure online interactions, cryptography relies on mathematical principles that are simple to understand but extremely difficult to break, and the science behind the problem and solution. As technology advances, cryptography continues to evolve to address new threats, and understanding its mathematical and scientific foundations not only emphasizes its importance but also illustrates how mathematical ideas and scientific understanding profoundly impact the world.

References
Fortinet. “What Is Cryptography? Definition, Importance, Types.” Fortinet, 2023, www.fortinet.com/resources/cyberglossary/what-is-cryptography.
GeeksforGeeks. “Cryptography and Its Types.” GeeksforGeeks, 8 July 2019, www.geeksforgeeks.org/computer-networks/cryptography-and-its-types/.
“Quantum Attack Resource Estimate: Using Shor’s Algorithm to Break RSA vs DH/DSA vs ECC - Kudelski Security Research Center.” Kudelskisecurity.com, 2017, kudelskisecurity.com/research/quantum-attack-resource-estimate-using-shors-algorithm-to-break-rsa-vs-dh-dsa-vs-ecc.
The. “Understand the Math.” Understand the Math, 2024, www.understandthemath.com/blog/math-behind-cryptography.
“Understanding Cryptography: The Science of Securing Information.” City.ac.uk, 2025, technology.online.city.ac.uk/blogs/understanding-cryptography-the-science-of-securing-information/.




Comments